Briç Güvenlik: The interoperability trilemma of bridges needs a rethink. Data Journalist Daniel C. Park explains what is in the pipeline to prevent bridge hacks.
At Göçebe, we are working on a new category of bridges. They are designed to reduce the worst-case scenario of a bridge hack. We are trading-off latency for security. We feel that this is a more compelling situation, against a backdrop of bridges that have been robbed of a billion dollars this quarter alone.
Successful exploits of QBridge ($80m), Wormhole ($326m), ve Ronin ($624m) are powerful reminders that the birlikte çalışabilirlik üçlemesi of bridges needs a total rethink. A desire for anti-fraud features has intensified among bridge users. And that’s the problem we are solving.
kullanma Kovalent application programming interface (API), we can trace how bridge users on Ethereum and Moonbeam are responding to Nomad’s security appeal. Nomad’s post-launch figures, such as total unique addresses and TVL per user, signal a promising outlook for optimistic systems.
Bridge Security: Has cross-chain bridge security reached an impasse?
At Nomad, we are challenging the proliferating narrative that cross-chain bridges, despite their enormous economic utility, had become too risk-prone to exploits. Even a 51% attack on a small-cap chain, due to overlapping derivatives, can compromise interconnected chains.
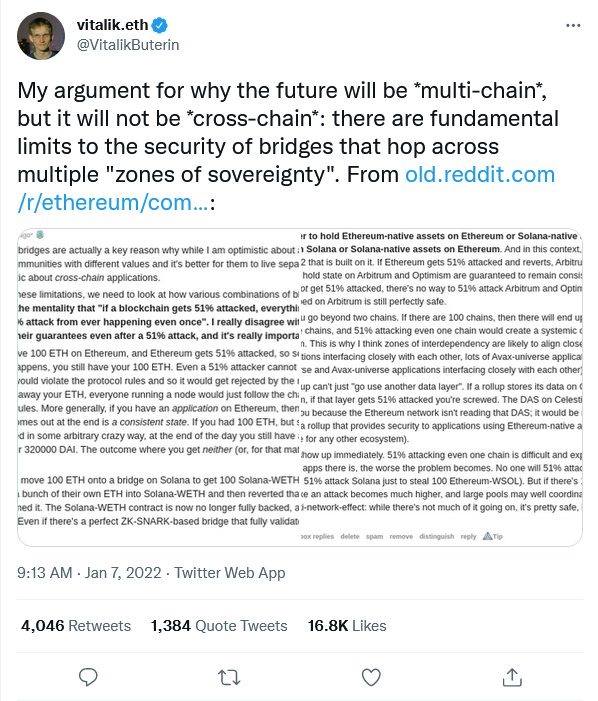
Vitalik had pioneered and floated bu bakış açısı in January this year, citing “fundamental security limits of bridges,” and that cross-chain bridges should be regarded as an interim solution to advancing chain interoperability.
However, Nomad’s radical features, such as optimistic verification, advance a counter-narrative to this growing perception that bridge technology had reached an impasse.
Sacrificing latency for absolute security
Echoing the predicament observed in the ölçeklenebilirlik üçlemesi, bridges too must traditionally forego at least one of three desirable properties – trust minimization, generalizability (support transferring arbitrary data), and extensibility (across as many heterogeneous chains).
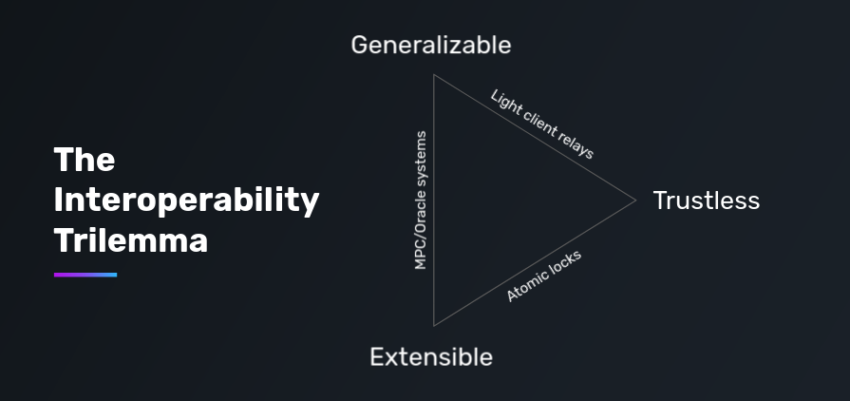
Departing from the trilemma, Nomad unorthodoxically sacrifices latency as a means to provide a security-first interoperability solution. Patterned after iyimser toplamalar, Nomad minimizes the visibility of attestation on-chain, and accepts it as valid within a fraud-proof window of ~30 minutes.
Bridge Security: Insuring against the loss of any funds
Within this timeframe, data on Nomad is essentially cycled between an Updater, who signs and uploads the data to the origin chain; and a bakıcı, who detects and reacts to faulty attestations.
Uniquely, departing from classical optimistic protocols, Nomad necessitates that an Updater submit a bonded stake on the origin chain. This insures Nomad’s security against the possibility of even a trusted Updater corroborating fraud.
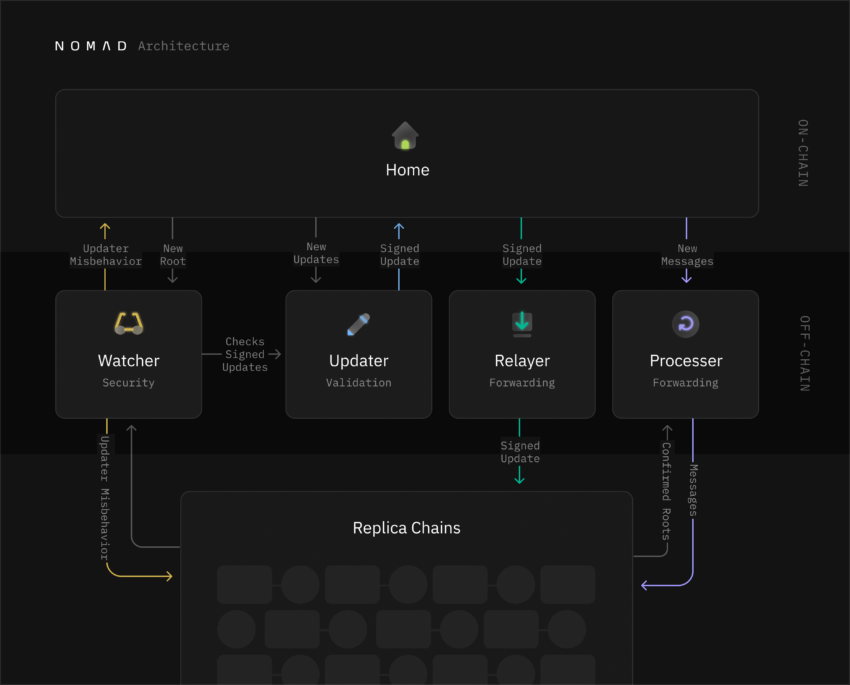
In the event an honest Watcher proves fraud, the communication line from the origin to the destination chain is immediately severed, slashing the Updater’s bonds; and channeling the retrieved funds to the disputing Watcher.
That means, the bridge will be shut down, instead of users being robbed of any funds. Absence of fraud, alternatively, facilitates the data towards the destination chain as originally intended.
Fooling hackers with a single honest verifier
Zaten, Gökkuşağı köprüsü için YAKIN protokol is corroborating the security merits of optimistic designs, having repelled an attack on May first this year.
Prominently, Nomad’s bridge security follows a single honest verifier assumption, only requiring 1 of n actor(s) to validate transactions. In contrast, externally verified bridges are typically based on an honest majority assumption, where m of n participant(s) oversee the validation scheme.
Because of this, enabling permissionless Watchers that could be deployed by any Nomad user would make it impossible for hackers to know there is not at least one-single Watcher overseeing every transaction.
Optimistic systems, in this way, raises the economic cost for malicious actors (gaz ücretleri and the stake bonded by the Updater) to compromise their targets, with very little guarantee.
How is Nomad’s security proposition appealing to bridge users?
The technology Nomad builds on is battle-tested. Through Covalent’s unified API, we can see whether Nomad is properly capitalizing on its security appeals and accumulating a dedicated user base.
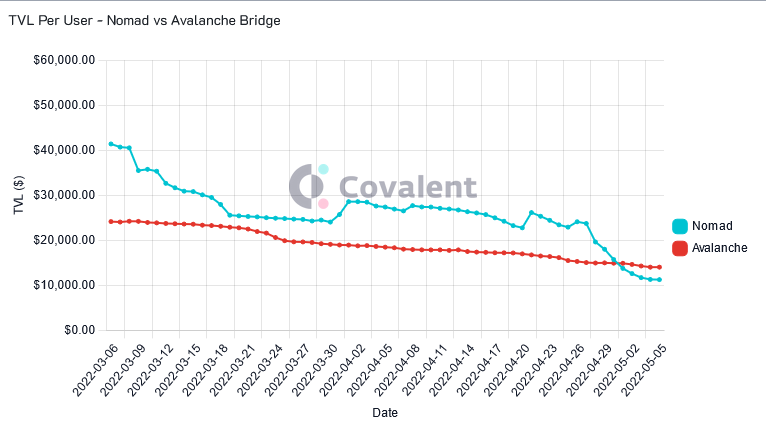
Notably, compared to the more commercially mature çığ köprüsü, Nomad’s TVL per user averaged higher numbers. Recording between $30-$40k daily per user since March 2022, Nomad’s figures outcompete that of çığ, which spanned between $20-$30k daily.
The disparity between the Avalanche Bridge and the newer Nomad bridge suggests a deep trust in Nomad’s security and anti-fraud features among bridge users.
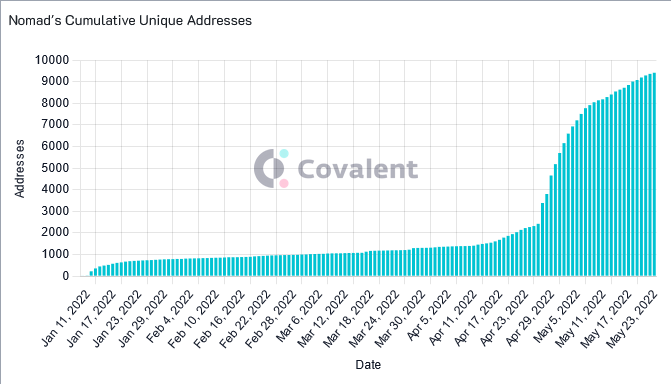
Likewise, the first week of May alone saw 5,000 new addresses bridge with Nomad. This is exponential growth considering Nomad took three-months to reach 3,000 unique addresses, illustrating that Nomad’s security appeals are marketable and perceived valuable by a wider array of bridge users.
Using Connext to solve Nomad’s latency shortcomings
The slow latency of ~30 minutes remains a glaring drawback for the bridge. Because of this, Nomad partnered with Bağlantı, a cross chain liquidity network built on Ethereum as a L2 with much faster speeds.
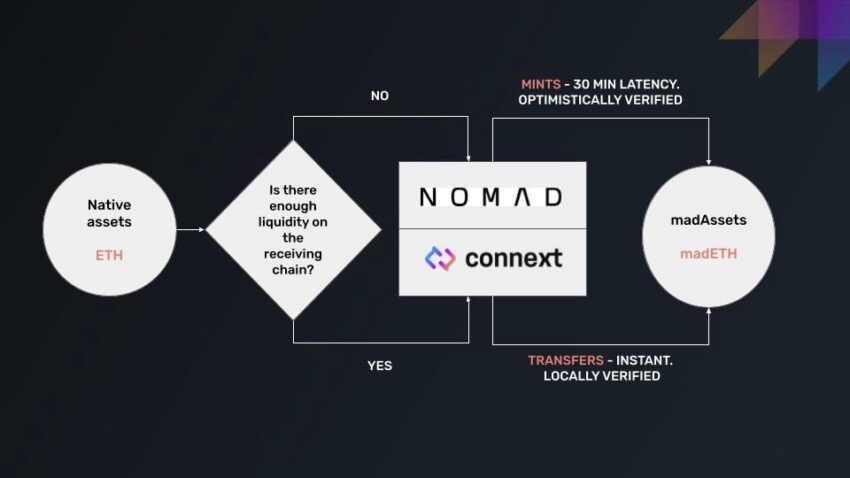
The modularity of layering Nomad and Connext together is another radical reapproach to the trilemma their partnership introduced. Connext properly fills the gap in speed Nomad was forced to forgo.
By doing so, the harmonized dual-system dynamically routes and modulates transactions, depending on the size of the asset being transferred and the liquidity pool corresponding to the asset.
Cross-chain bridge security is evolving with “stackable” bridges
As their synergy scales into a larger operation, Nomad can be tailored to focus further on institutional capital. Whereas, end users opting for smaller and faster transactions can be routed via Connext.
The security appeals of Nomad and corresponding growth figures, in retrospect, illustrate a pivotal moment in the history of cross-chain bridges.
We are aiming for a departure from the series of high-profile bridge hacks stunting the advancement of chain interoperability.
Yazar hakkında

Daniel C. Park originally entered the Web3 space in 2019 researching blockchain’s utility in humanitarian affairs with Starling Lab at Stanford. He currently works as a Data Journalist at Covalent.
Got something to say about bridge security or anything else? Bize yazın veya tartışmaya katılın Telgraf kanalı. Bizi de yakalayabilirsiniz Tik Tok, Facebookya da Twitter.
Feragatname
Web sitemizde yer alan tüm bilgiler iyi niyetle ve yalnızca genel bilgi amaçlı yayınlanmaktadır. Okuyucunun web sitemizde bulunan bilgilere göre yapacağı herhangi bir eylem kesinlikle kendi sorumluluğundadır.
Source: https://beincrypto.com/bridge-security-new-tech-means-bridge-hacks-should-be-just-a-memory/